Fancy Bear, the advanced hacking team researchers say is tied to the Russian govt, is actively exploiting a recently revived method that provides attackers a stealthy means of infecting computers using Ms office documents, security researchers said in the week.
Fancy Bear is one of the 2 Russian-sponsored hacking outfits researchers say breached Democratic National Committee networks ahead of last year’s presidential election. The team was recently caught sending a Word document that abuses a feature referred to as Dynamic Data Exchange. DDE allows a file to execute code save in another file and allows applications to transfer updates as new data becomes available.
In a blog post published Tuesday, Trend micro researchers said Fancy Bear was sending a document titled IsisAttackInNewYork.docx that abused the DDE feature. Once opened, the file connects to a main control server to download and installs a 1st-stage of the piece of malware (Seduploader) it on a target’s pc’s. DDE’s potential as an infection technique has been known for years, but a post published last month by security firm SensePost has revived interest in it. The post showed however DDE could be abused to install malware using Word files that went undetected by anti-virus programs.
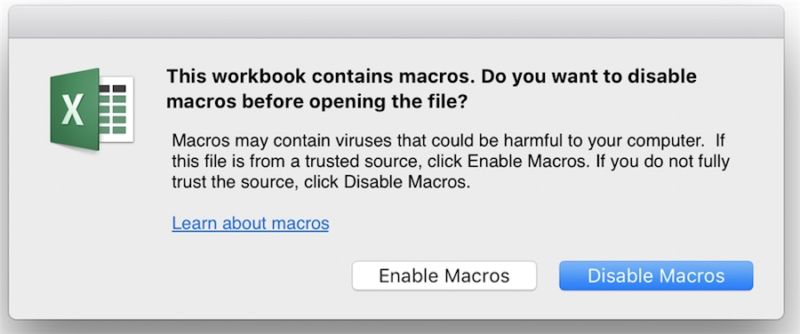
A day after Trend micro published its report regarding Fancy Bear, Microsoft posted an advisory explaining how office users will protect themselves from such attacks. the simplest way to keep safe is to remain wary of unfamiliar messages that get displayed once opening a document. As SensePost 1st disclosed, before the DDE feature will be used, users can see a dialog box that appears something just like the following:

If targets click yes, they will see a prompt that looks something like this:
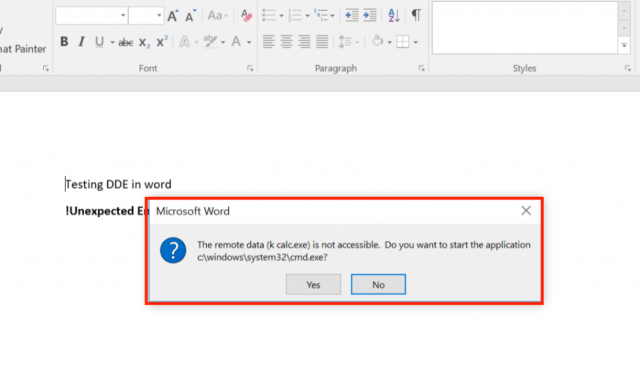
The malicious payload can only execute when a user has clicked yes to both warnings.
The Microsoft advisory also explains, however, more technically advanced users will change settings in the Windows registry to disable automatic updating of data from one file to another.
Fancy Bear is not the 1st group to actively exploit DDE in the wild. some weeks after the SensePost post went live, researchers reported attackers were abusing the feature to install the Locky ransomware.
Many researchers have remarked on the power of the DDE-enabled attacks to spread malware through office documents without the macros. The novelty is probably going to create DDE effective in some settings, given the growing awareness of the risks, macros pose. but ultimately, the DDE mechanism comes with its own telltale signs. people must learn to recognize them presently that DDE attacks are growing more common.
Google Street View new algorithm correcting misalignment’s in existing panoramas
Upcoming Android update will highlight battery draining apps